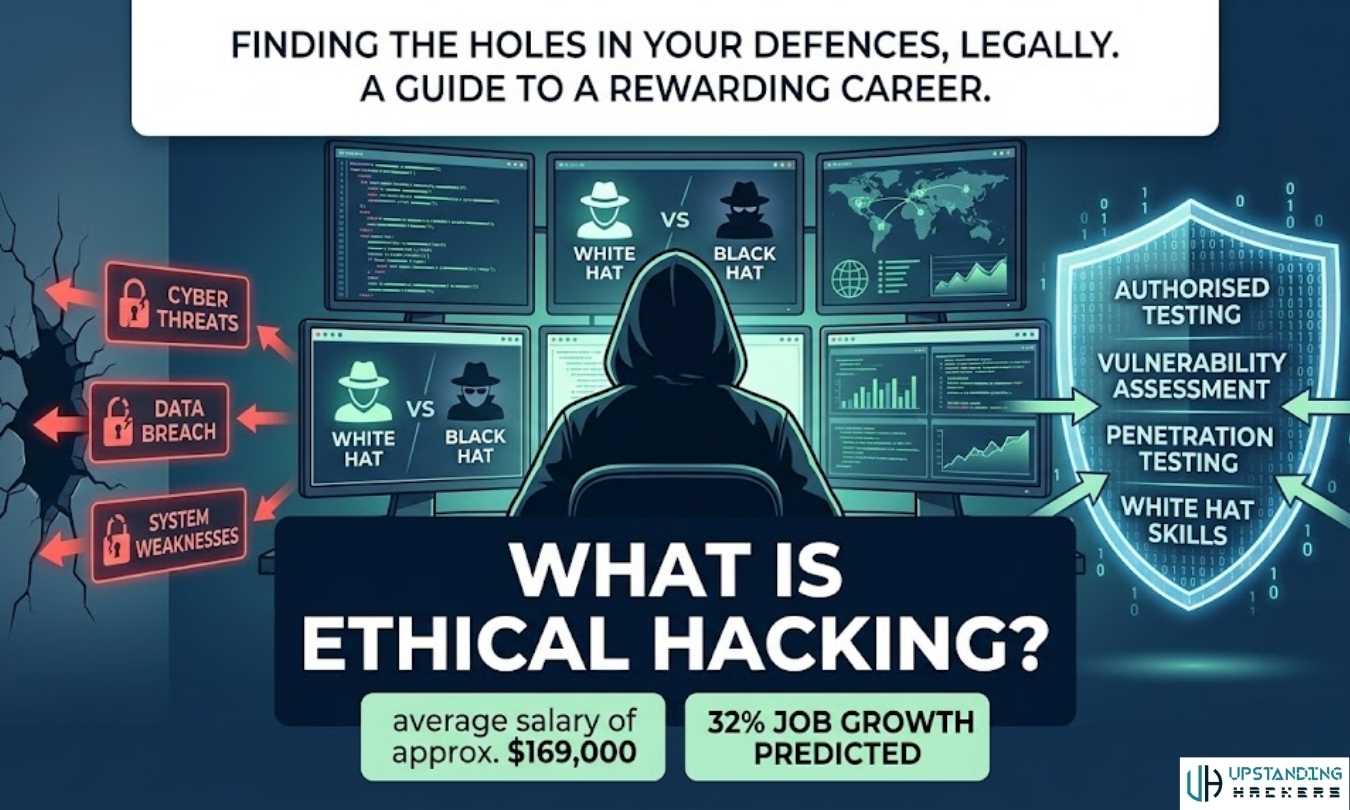
What Is Ethical Hacking? The Complete Beginner-to-Pro Guide (2026)
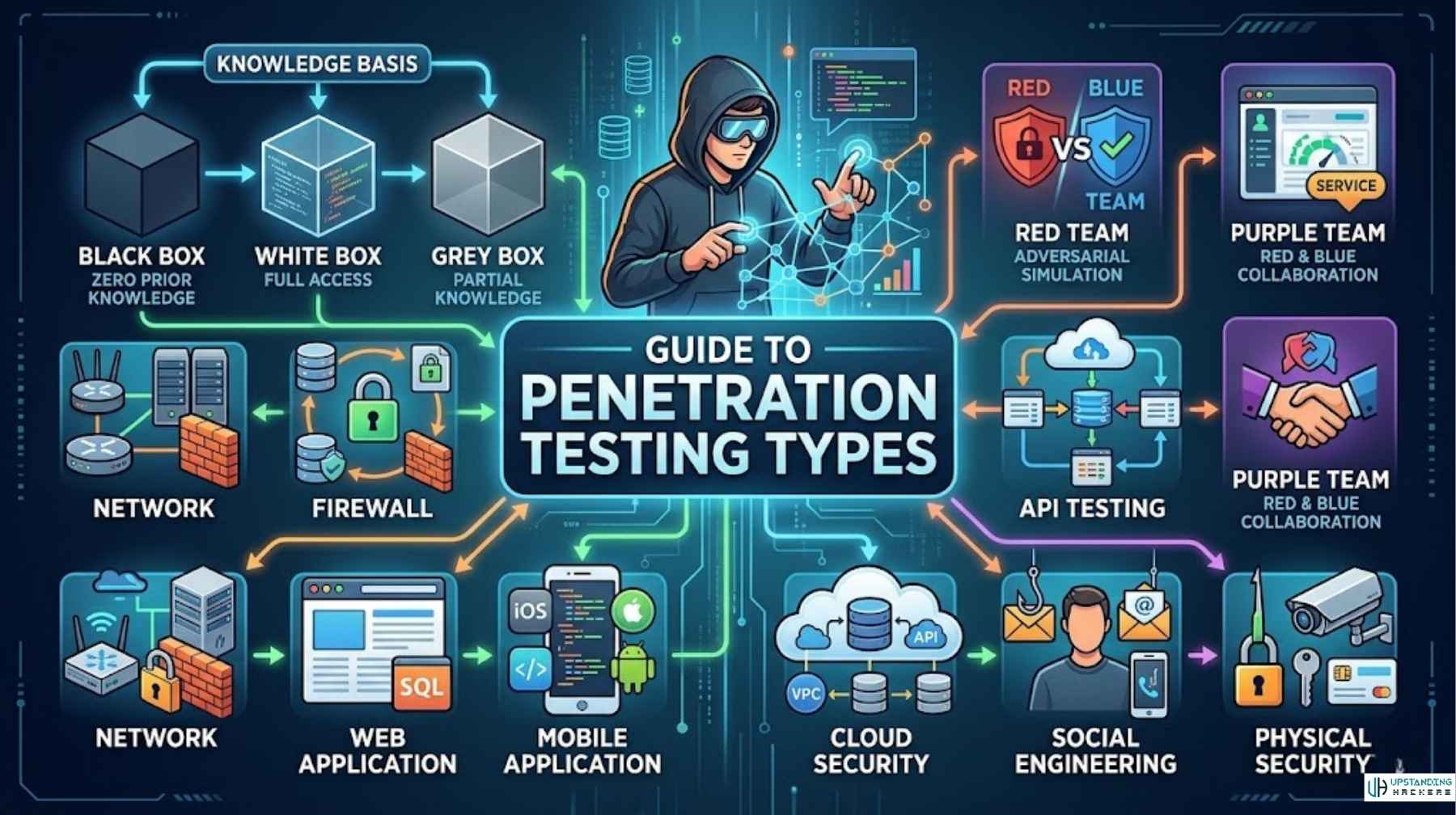
Ethical hacking is one of the most in-demand skills in the world right now. Cybercrime costs are projected to reach $23 trillion annually by 2027, and organisations are desperately searching for profe...