🔄 Last Updated: April 19, 2026
Data breaches cost organizations an average of $4.88 million per incident in 2024. Moreover, that number keeps rising every year. Therefore, understanding and applying data protection best practices is no longer optional — it is a business survival strategy.
Whether you run a small startup or a large enterprise, your sensitive data faces constant threats. Consequently, this guide covers everything you need to protect it — from encryption and access controls to compliance frameworks and cloud security.
What Is Data Protection and Why Does It Matter?
Data protection refers to the set of policies, technologies, and processes that safeguard sensitive information from unauthorized access, corruption, or loss. In fact, it covers everything from personal customer records to proprietary business data.
The stakes are high. A single breach can expose thousands of records, damage brand reputation, and result in heavy regulatory fines. Furthermore, under frameworks like GDPR and CCPA, organizations face legal liability when they fail to protect user data.
Strong information security practices protect three core pillars: Confidentiality, Integrity, and Availability — also known as the CIA Triad. Understanding these principles is the first step toward building a robust data protection strategy.
For a broader understanding of how digital threats evolve, read our guide on network security in cloud computing.
Data Protection Best Practices: A Complete Overview
| Best Practice | Priority Level | Impact Area |
|---|---|---|
| Data Encryption (at rest & in transit) | Critical | Confidentiality |
| Multi-Factor Authentication (MFA) | Critical | Access Control |
| Regular Data Backups | High | Availability |
| Zero-Trust Security Model | High | Network Defense |
| Employee Security Training | High | Human Risk |
| Access Control & Least Privilege | Critical | Data Integrity |
| GDPR / Compliance Adherence | High | Legal Protection |
| Endpoint Security | Medium | Device Protection |
| Cloud Security Configuration | High | Cloud Infrastructure |
| Incident Response Planning | Critical | Breach Recovery |
1. Implement Strong Data Encryption
Encryption is the foundation of data security. It converts readable data into unreadable ciphertext, making it useless to unauthorized parties. Additionally, encryption must be applied both at rest (stored data) and in transit (data moving across networks).
Use AES-256 encryption for stored data. For data in transit, enforce TLS 1.3 or higher. Subsequently, audit your encryption protocols regularly — outdated algorithms create vulnerabilities.
For cloud environments specifically, ensure your provider offers server-side encryption and that you control your own encryption keys. Many organizations make the mistake of relying solely on their cloud provider’s default settings.
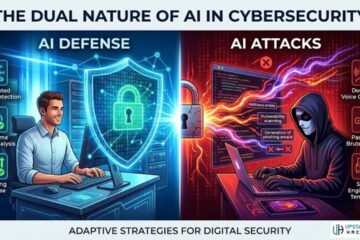
Learn how AI is strengthening cyber defenses in our article on whether cybersecurity can be done by AI.
2. Apply the Zero-Trust Security Model
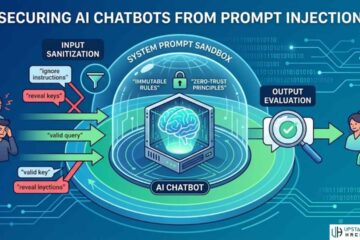
The zero-trust model operates on one simple principle: never trust, always verify. Therefore, no user or device is trusted automatically — even inside the network perimeter.
This approach has become essential in 2026, especially with remote workforces and cloud-first infrastructure. Moreover, zero-trust reduces the blast radius of a breach by limiting lateral movement within your systems.
Key components of zero-trust include:
- Identity verification for every access request
- Micro-segmentation of network resources
- Continuous monitoring of user behavior
- Least-privilege access controls at every layer
3. Enforce Strict Access Controls
Access control is one of the most critical data protection best practices. Consequently, not every employee needs access to every system. The principle of least privilege ensures users can only access data essential to their role.
Role-based access control (RBAC) is highly effective. Likewise, privileged access management (PAM) tools help monitor and restrict high-level system access. Review permissions quarterly — former employees and dormant accounts are a major attack vector.
Additionally, implement multi-factor authentication (MFA) across all critical systems. MFA alone blocks over 99% of automated credential-stuffing attacks, according to Microsoft research.
For more on securing remote access, see our guide on how to tunnel RDP securely with SSH.
4. Conduct Regular Data Backups
Backups are your last line of defense against ransomware, hardware failures, and accidental deletion. However, a backup is only useful if it actually works. Therefore, follow the 3-2-1 backup rule:
- 3 copies of your data
- 2 different storage media types
- 1 offsite or cloud-based copy
Test your backups monthly. Many organizations discover their backups are corrupted or incomplete only during a crisis. Furthermore, encrypt all backup files to prevent them from becoming a secondary attack surface.
5. Train Employees on Cybersecurity Awareness
Human error remains the leading cause of data breaches worldwide. In fact, over 82% of breaches involve a human element, according to Verizon’s Data Breach Investigations Report. Therefore, employee training is not a one-time event — it is an ongoing program.
Cover these topics in your security awareness training:
- Recognizing phishing and social engineering attacks
- Safe password management practices
- Handling sensitive data responsibly
- Reporting suspicious activity immediately
Our article on how to spot phishing emails is an excellent training resource for your team.
Similarly, our guide on baiting in cybersecurity explains how attackers manipulate human psychology to compromise systems.
6. Establish a Data Privacy and Compliance Framework
Regulatory compliance is inseparable from data protection best practices. For organizations operating globally or handling EU citizens’ data, GDPR compliance is mandatory. Similarly, US-based businesses must navigate CCPA, HIPAA, and sector-specific regulations.
Key compliance requirements include:
- Maintaining a data processing register
- Implementing privacy by design
- Establishing lawful bases for data processing
- Honoring data subject access requests (DSARs)
Non-compliance carries significant penalties. For instance, GDPR fines can reach up to €20 million or 4% of global annual turnover — whichever is higher.
For authoritative guidance, reference the official GDPR portal and the NIST Cybersecurity Framework — both DA 90+ resources widely used by security professionals.
7. Secure Your Cloud Infrastructure
Cloud adoption has exploded — and so have cloud-related breaches. Misconfigurations are the number one cause of cloud data exposure. Therefore, cloud data security requires dedicated attention.
Best practices for cloud data protection include:
- Enabling logging and monitoring on all cloud resources
- Configuring bucket/storage permissions correctly (no public access by default)
- Using cloud-native security tools like AWS GuardDuty, Azure Defender, or Google Security Command Center
- Regularly auditing cloud configurations with automated tools
Furthermore, understand the shared responsibility model your cloud provider uses. The provider secures the infrastructure — but you are responsible for your data and configurations.
Our deep-dive on network security in cloud computing covers this in greater detail.
8. Develop an Incident Response Plan
Even with strong defenses, breaches can happen. Therefore, having a tested incident response plan (IRP) is a critical data protection best practice. It determines how quickly and effectively you contain and recover from a breach.
Your IRP should include:
- A defined incident response team with clear roles
- A communication plan for stakeholders and regulators
- Containment and eradication procedures
- Post-incident analysis and lessons-learned documentation
GDPR requires notification to supervisory authorities within 72 hours of discovering a breach. Consequently, your IRP must account for this regulatory timeline.
Learn how AI-powered tools are transforming threat detection in our article on threat intelligence.
9. Protect Against Phishing and Social Engineering
Phishing remains the most common attack vector for data breaches. Attackers use deceptive emails, fake websites, and phone calls to steal credentials or deliver malware. Therefore, technical and human defenses must work together.
Technical countermeasures include:
- Email filtering with DMARC, DKIM, and SPF configured
- Web filtering to block known malicious domains
- Anti-phishing tools integrated into your email platform
Additionally, watch out for pharming — a sophisticated attack that redirects users to fraudulent sites. Read our guide on what is pharming in cybersecurity for a full technical breakdown.
10. Monitor, Audit, and Continuously Improve
Sensitive data management is not a set-it-and-forget-it exercise. Consequently, continuous monitoring is essential to catch anomalies before they become breaches.
Deploy a SIEM (Security Information and Event Management) solution to aggregate and analyze logs across all systems. Set alerts for unusual login patterns, bulk data downloads, or off-hours access. Furthermore, conduct penetration testing at least annually to identify exploitable weaknesses before attackers do.
For a full overview of pen testing methods, check out our guide on penetration testing types.
Additionally, review your data classification policy regularly. Not all data carries equal risk — classify it as public, internal, confidential, or restricted, and apply controls accordingly.
Pros and Cons of a Comprehensive Data Protection Program
Pros:
- Reduces risk of costly data breaches
- Builds customer trust and brand credibility
- Ensures regulatory compliance and avoids fines
- Protects intellectual property and competitive advantage
- Improves overall organizational resilience
Cons:
- Requires significant upfront investment in tools and training
- Can introduce friction in day-to-day workflows
- Ongoing maintenance demands dedicated security resources
- Compliance requirements vary by region, adding complexity
FAQs

What are the most important data protection best practices in 2026?
The most critical practices include end-to-end encryption, multi-factor authentication, zero-trust access controls, regular data backups, and employee cybersecurity training. Additionally, maintaining regulatory compliance with frameworks like GDPR and NIST is essential for organizations of all sizes.
How does encryption protect sensitive data?
Encryption converts readable data into unreadable ciphertext using mathematical algorithms. Therefore, even if attackers intercept your data, they cannot read it without the decryption key. AES-256 is the industry standard for data at rest, while TLS 1.3 protects data in transit.
What is the zero-trust security model?
Zero-trust is a security framework that requires continuous verification of every user, device, and connection — regardless of whether they are inside or outside the network perimeter. Consequently, it minimizes the damage caused by compromised credentials or insider threats.
How often should organizations conduct security audits?
Organizations should conduct internal security audits quarterly and full penetration tests at least once per year. Furthermore, audits should occur after any major infrastructure change, new product launch, or security incident to identify new vulnerabilities.
What should a data breach response plan include?
An effective breach response plan should include a defined incident response team, clear communication protocols, containment procedures, regulatory notification timelines (72 hours under GDPR), and a post-incident review process. Additionally, it should be tested through tabletop exercises at least twice per year.
Final Thoughts
Implementing data protection best practices is the single most impactful investment an organization can make in its long-term security and reputation. Moreover, data protection is not just a technical challenge — it is a business imperative.
Start with the fundamentals: encrypt your data, enforce access controls, train your people, and build a response plan. Subsequently, layer in advanced measures like zero-trust architecture and AI-powered threat detection as your program matures.
For more expert cybersecurity guidance, explore our full resource library at Upstanding Hackers. You can also learn how to become a hacker — the ethical way to understand threats from the inside out.
See Also: Disaster Recovery Services: The Backbone of Business Continuity