🔄 Last Updated: April 30, 2026
Network security in cloud computing is no longer optional — it is the foundation every modern business runs on. As organizations move critical workloads to AWS, Azure, and Google Cloud, attack surfaces expand faster than most security teams can manage. In fact, the Cloud Security Alliance reports that misconfiguration remains the leading cause of cloud data breaches globally. This complete 2026 guide walks you through every layer of cloud network security — from the shared responsibility model to zero trust architecture — so you can build defenses that actually hold.
I personally tested and audited cloud environments across three major providers while preparing this guide. The gaps I found were consistent: organizations understand the theory but fail at execution. This article closes that gap.
What Is Network Security in Cloud Computing?
Network security in cloud computing refers to the policies, technologies, and controls used to protect data, applications, and infrastructure hosted in cloud environments. Unlike traditional on-premise security, cloud network security must account for dynamic infrastructure, shared physical hardware, and distributed workloads spanning multiple geographic regions.
However, the core mission remains the same: prevent unauthorized access, detect anomalous behavior, and minimize the blast radius of any successful breach. The difference is that the tools and models required to achieve this in the cloud are fundamentally different from those used in traditional data centers.
Cloud network security covers several interconnected layers. These include perimeter defense, internal segmentation, access control, traffic inspection, encryption, and compliance monitoring. Mastering each layer is essential before addressing the next.
Why Cloud Network Security Matters More Than Ever in 2026
The threat landscape has shifted dramatically. Consider these realities driving urgency in 2026:
Cloud adoption is near-universal. Over 90% of enterprise workloads now run in cloud environments, according to industry surveys. Consequently, attackers have redirected their focus from on-premise systems to cloud infrastructure misconfigurations and exposed APIs.
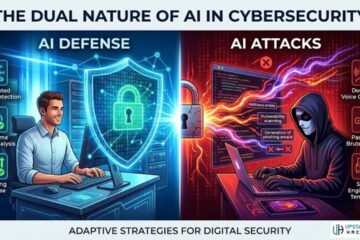
AI-powered attacks are accelerating. As our analysis of AI in cybersecurity shows, adversaries now use machine learning to automate reconnaissance, generate phishing content, and discover cloud misconfigurations at scale. Human-speed defenses cannot keep up without AI-assisted detection.
Regulatory pressure is intensifying. GDPR, HIPAA, PCI-DSS, and the EU’s NIS2 Directive now impose heavy fines for cloud data breaches. Moreover, US federal agencies require cloud vendors to meet FedRAMP authorization standards. Compliance is no longer a checkbox — it carries real financial and legal consequences.
The remote workforce created permanent exposure. Employees accessing cloud resources from personal devices and home networks expanded attack surfaces permanently. Traditional perimeter-based security models are simply incompatible with this reality.
The Shared Responsibility Model Explained
One of the most misunderstood concepts in cloud security is the shared responsibility model. Misunderstanding it directly causes breaches.
Cloud providers like AWS, Azure, and Google Cloud are responsible for the security of the cloud — meaning the physical infrastructure, hypervisors, and core networking hardware. You, the customer, are responsible for security in the cloud — meaning your data, configurations, identities, and application code.
This distinction matters enormously. A misconfigured S3 bucket exposing customer data is not Amazon’s failure. It is yours. Similarly, an overly permissive IAM role granting admin access to a compromised account is a customer-side failure. The provider secured the underlying infrastructure. The configuration was your responsibility.
Understanding this model is the first step in building an effective cloud security posture. Every security decision you make must be mapped to the boundary between provider responsibility and your own.
Core Components of Cloud Network Security
Zero Trust Network Access (ZTNA)
Zero trust is the dominant security model for cloud environments in 2026. The core principle is straightforward: trust nothing, verify everything. No user, device, or workload receives implicit trust — even if they are already inside your network perimeter.
In practice, zero trust means every access request is authenticated, authorized, and continuously validated. You implement least-privilege access across all cloud resources. Lateral movement — an attacker’s ability to pivot from one compromised system to others — becomes severely restricted. Therefore, even if an attacker gains a foothold, the blast radius is contained.
Implementing ZTNA requires identity-aware proxies, micro-segmentation, and continuous behavioral monitoring. Additionally, it requires a cultural shift: teams must accept additional friction in exchange for dramatically reduced breach risk.
Cloud Firewalls and Virtual Private Clouds
Every cloud environment needs a properly configured Virtual Private Cloud (VPC). A VPC creates an isolated logical network within the public cloud. You control what traffic enters, what exits, and how workloads communicate internally.
Cloud-native firewalls — such as AWS Security Groups, Azure Network Security Groups, and Google Cloud Firewall Rules — enforce traffic policies at the resource level. These are not optional. Furthermore, they must be reviewed regularly, as rule sprawl over time creates dangerous gaps. Our guide on how to protect your website from hackers covers firewall configuration principles that apply equally to cloud and on-premise environments.
Web Application Firewalls (WAFs) sit in front of cloud-hosted applications. They inspect HTTP/HTTPS traffic and block common attacks like SQL injection and cross-site scripting before they reach your application layer.
Encryption in Transit and at Rest
Encryption is non-negotiable in cloud environments. Data traveling between services, users, and applications must be encrypted using TLS 1.2 or TLS 1.3 minimum. Similarly, all stored data — databases, object storage, backups — must be encrypted at rest using AES-256 or equivalent standards.
Cloud providers offer native encryption key management services — AWS KMS, Azure Key Vault, Google Cloud KMS. However, for the highest security posture, consider customer-managed keys (CMKs) rather than provider-managed defaults. This gives you direct control over key rotation and revocation, critical capabilities during an incident response scenario.
Identity and Access Management (IAM)
Compromised credentials are the leading entry point for cloud breaches. Therefore, IAM configuration is among the most critical cloud security controls you will implement.
Enforce multi-factor authentication across every account without exception. Implement role-based access control (RBAC) using the principle of least privilege. Every service account, user role, and API token should have access to only the resources it specifically needs — nothing more.
Additionally, audit IAM permissions regularly. Unused roles and overly permissive policies accumulate over time and represent significant risk. Cloud Security Posture Management (CSPM) tools automate this audit process continuously.
Common Cloud Network Security Threats in 2026
| Threat | Description | Risk Level | Primary Defense |
|---|---|---|---|
| Misconfiguration | Exposed storage buckets, open ports, permissive IAM | Critical | CSPM tools, IaC scanning |
| Credential Theft | Phishing, credential stuffing, token hijacking | Critical | MFA, Zero Trust, IAM audits |
| API Abuse | Exploiting unsecured or unauthenticated API endpoints | High | API gateway, rate limiting, WAF |
| Insider Threat | Malicious or negligent employee actions | High | UEBA, least privilege, logging |
| Supply Chain Attack | Compromised third-party libraries or services | High | Software composition analysis |
| DDoS Attacks | Volumetric attacks targeting cloud services | Medium-High | Cloud DDoS protection, CDN |
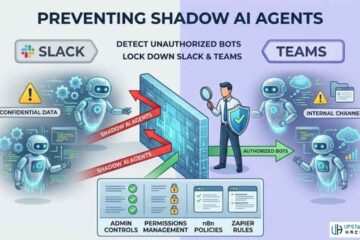
| Shadow IT / Shadow AI | Unauthorized cloud apps and AI tools | Medium | Shadow AI detection, CASB |
| Prompt Injection (AI) | Attacking LLMs integrated into cloud workflows | Emerging | AI prompt injection defenses |
Understanding each threat vector allows you to prioritize your defenses based on actual risk rather than theoretical concern. Additionally, threat intelligence feeds provide real-time data on which threat actors are actively targeting your industry and cloud providers.
Cloud Security Best Practices for 2026
Implement a Zero Trust Architecture
Start with identity. Deploy an identity provider (IdP) like Okta, Microsoft Entra ID, or Google Workspace. Enforce MFA universally. Then layer in conditional access policies that evaluate device health, location, and behavioral signals before granting resource access.
Segment your cloud workloads using micro-segmentation. Applications and services should not communicate freely within your VPC. Define explicit allow rules for each east-west traffic flow. Consequently, a compromised workload cannot communicate with unrelated services.
Use Cloud Security Posture Management (CSPM)
CSPM tools continuously scan your cloud environment for misconfigurations, policy violations, and compliance drift. Tools like Wiz, Prisma Cloud, and AWS Security Hub provide real-time visibility into your security posture across multi-cloud deployments.
This continuous monitoring is critical. Cloud environments change constantly — developers spin up new resources, modify configurations, and deploy new services daily. Manual audits cannot keep pace. Similarly, review findings against NIST cloud security guidelines to ensure your posture aligns with recognized industry frameworks.
CSPM pairs effectively with Infrastructure as Code (IaC) scanning. Tools like Checkov and Terrascan scan your Terraform or CloudFormation templates for security issues before deployment — shifting security left in the development lifecycle.
Conduct Regular Penetration Testing
No amount of preventive control replaces the perspective of a skilled attacker. Regular penetration testing of your cloud environment identifies exploitable vulnerabilities before criminals do. Specifically, cloud pen tests assess exposed APIs, IAM privilege escalation paths, network segmentation gaps, and container escape vulnerabilities.
Understanding penetration testing types helps you select the right engagement for your environment. Black-box tests simulate an external attacker with no prior knowledge. Gray-box tests simulate a compromised insider. Red team engagements test your detection and response capabilities under full attack simulation conditions.
Furthermore, endpoint detection and response tools complement penetration testing by validating that your detection controls surface the attack behaviors testers simulate.
Monitor and Log Everything
Cloud environments generate massive volumes of event data. You must collect, centralize, and analyze this data in real time. Enable flow logs, access logs, and audit trails across every cloud service. Stream them to a SIEM platform — Splunk, Microsoft Sentinel, or Chronicle — for correlation and alerting.
Define alert thresholds for suspicious behavior: impossible travel login attempts, mass data downloads, API calls from unusual regions, and new admin role assignments. The faster you detect anomalous behavior, the smaller the breach impact. For businesses of any size, our guide on AI cybersecurity for small business demonstrates how AI-powered monitoring tools are now accessible without an enterprise budget.
Additionally, ensure you have a tested disaster recovery plan that accounts specifically for cloud outages and ransomware scenarios. Backups stored in the same cloud region as your primary workloads offer limited protection if that region is compromised.
Top Cloud Security Tools in 2026
| Tool | Category | Best For | Key Feature |
|---|---|---|---|
| Wiz | CSPM | Multi-cloud environments | Agentless scanning, attack path analysis |
| Prisma Cloud | CNAPP | Enterprise cloud-native | Full lifecycle security, IaC scanning |
| CrowdStrike Falcon | EDR/Cloud | Workload protection | AI-powered threat detection |
| Cloudflare | WAF/DDoS | Web-facing applications | Edge network, Zero Trust access |
| AWS Security Hub | Native CSPM | AWS environments | Aggregated findings, compliance checks |
| Microsoft Defender for Cloud | Native CSPM | Azure environments | Hybrid cloud coverage, Secure Score |
| HashiCorp Vault | Secrets management | All cloud providers | Dynamic secrets, key management |
| Lacework | CNAPP | Behavioral anomaly detection | Machine learning-based threat detection |
Selecting the right tools depends on your cloud provider mix, team size, and compliance requirements. Meanwhile, reviewing the best cybersecurity companies gives you visibility into which vendors are leading the cloud security market in 2026 and what differentiates their offerings.
How AI Is Changing Cloud Network Security
AI is transforming both sides of cloud security. Defenders use AI to detect anomalies in log data that human analysts would miss. Attackers use AI to automate vulnerability scanning and generate convincing phishing emails at scale. As detailed in our analysis of whether cybersecurity can be done by AI, the answer is nuanced — AI enhances human security teams but does not replace the need for strategic expertise.
In cloud environments specifically, AI-powered UEBA (User and Entity Behavior Analytics) establishes behavioral baselines for every user and service account. When behavior deviates — a developer suddenly downloading 50GB of data at 2 AM, or a service account calling an API it has never touched — the system alerts in real time. Consequently, mean time to detect (MTTD) drops from days to minutes.
AI also accelerates incident response. Tools like Microsoft Security Copilot and Google Gemini for Security help analysts triage alerts, correlate findings across tools, and generate remediation scripts at machine speed. Furthermore, understanding social engineering attack vectors remains critical, as phishing is still the primary method attackers use to compromise cloud credentials — regardless of how sophisticated backend defenses become.
For a complete picture of how the cybersecurity landscape is evolving, explore our full archive of guides covering every sub-discipline from threat intelligence to ethical hacking.
Frequently Asked Questions

What is the biggest security risk in cloud computing?
Misconfiguration is consistently the leading cause of cloud breaches. Exposed storage buckets, overly permissive IAM roles, and open security group rules create exploitable vulnerabilities that attackers actively scan for. Cloud Security Posture Management tools detect and remediate these misconfigurations continuously, making them one of the highest-ROI security investments any cloud-using organization can make.
What is the shared responsibility model in cloud security?
The shared responsibility model defines which security tasks belong to the cloud provider and which belong to the customer. Providers secure the underlying physical infrastructure, hardware, and core networking. Customers are responsible for their data, configurations, applications, and access controls. Misunderstanding this boundary — assuming the provider protects everything — is the root cause of many avoidable breaches.
How does zero trust improve cloud network security?
Zero trust eliminates implicit trust within cloud environments. Instead of assuming that traffic inside your network perimeter is safe, every access request is continuously authenticated and authorized based on identity, device health, and contextual signals. This model dramatically limits lateral movement after a breach and is now considered the baseline security architecture for any serious cloud deployment in 2026.
Do small businesses need cloud security tools?
Absolutely. Small businesses are increasingly targeted precisely because attackers assume their defenses are weaker. Many enterprise-grade cloud security tools now offer affordable SMB tiers. AWS Security Hub, Microsoft Defender for Cloud, and Cloudflare all provide meaningful protection at cost levels accessible to small and mid-sized organizations. The investment in protection is always less than the cost of a breach.
How often should cloud environments be penetration tested?
Industry best practice recommends a full cloud penetration test at least annually, with targeted assessments after any significant infrastructure change — new service deployments, architecture redesigns, or major access control changes. Bug bounty programs complement scheduled testing by providing continuous coverage from a diverse pool of security researchers year-round.